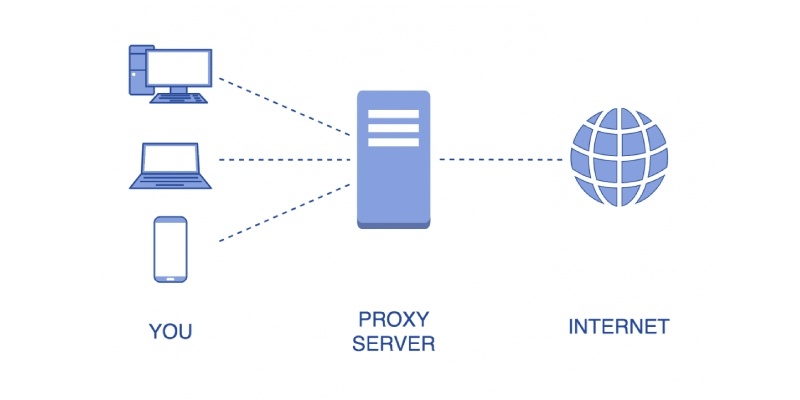
If you were to take a close look at your Internet settings, you may notice an available option is a ‘proxy.”
A proxy is nothing more than a tool your computer can use to protect you and your information. It can be thought of as a barrier; one that allows you to view websites and receive information from them without the website receiving your information.

In effect, the proxy server acts as a third party, filtering out requests according to the rules of the server.
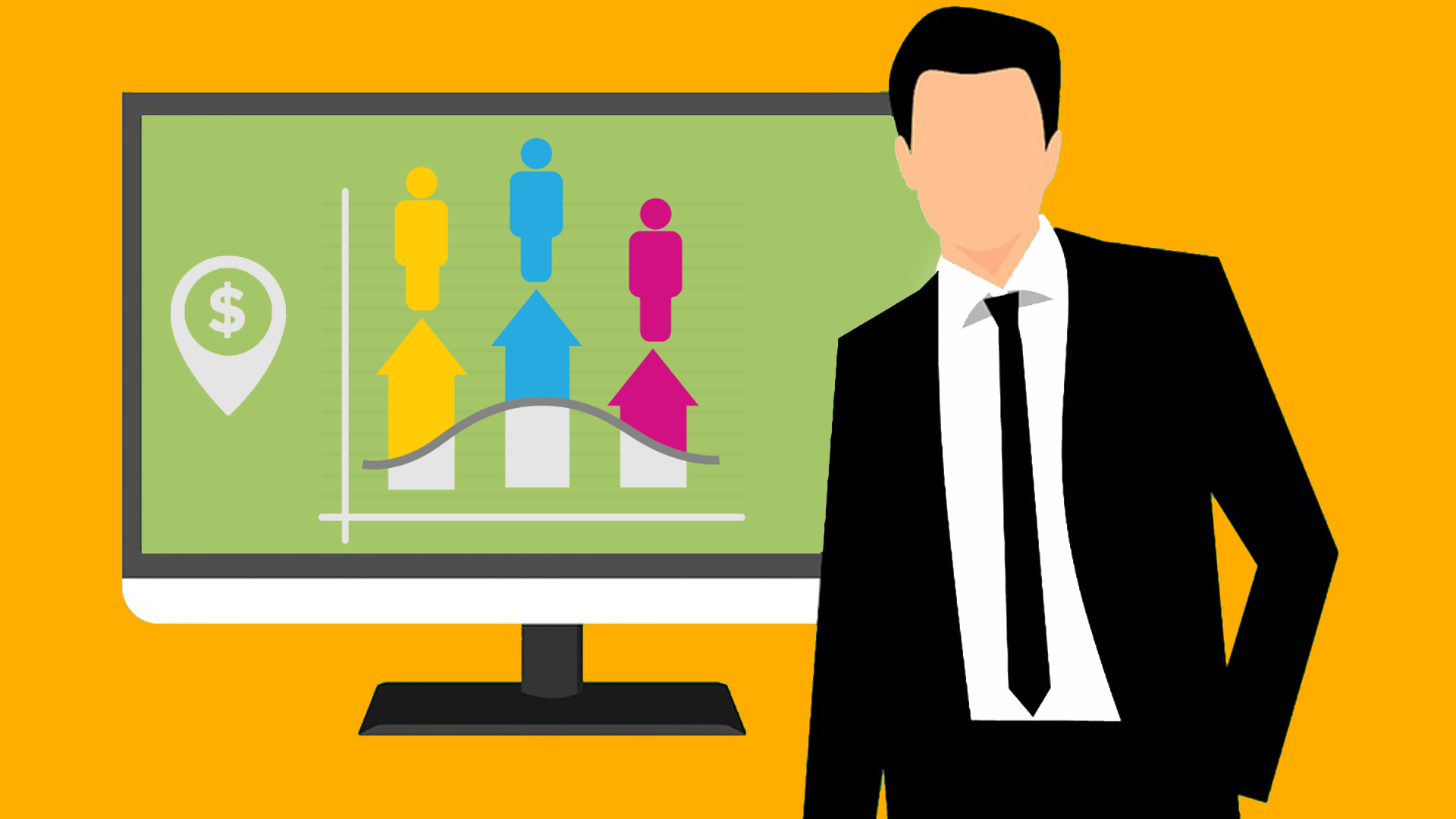
At its most basic level, the proxy server follows several key steps.
- The user connects to the proxy server
- The user requests information or a service. This could be a connection to a specific website or a file or other resource.
- The proxy server applies its filtering guidelines to the request.
- The verified request is sent to the appropriate server.
- The information or file is ‘collected’ and sent back to the user
Web Proxies Are Used For Security Purposes
Proxy servers are typically used for security purposes, although they are also used to block access and to apply content filtering rules, primarily to block sites that contain material that the user wants to be blocked (i.e. adult content).
Businesses often use proxy servers to audit employee usage or to protect against data or information leaks.
Types of Proxy Servers
Proxy servers work in various ways, in fact, there are several different types of proxies, each with its own specific purpose.
Caching Proxy Server
Caching proxies work by speeding up web requests. This is done by saving content made by an older request by the user.
In effect, a caching proxy server keeps copies of resources that are frequently requested.
This obviously has a significant positive impact on bandwidth cost and usage. It also has the effect of improving speed and performance.
Web Proxy
A web proxy is used primarily to filter content. Logs are typically produced which give information on specific websites accessed by users and can also be used to monitor overall bandwidth usage.
Hostile Proxy
This proxy is used to capture information about the web pages and forms that the user visits or fills out.
SIP Proxy Servers
These can be configured to complete tasks associated with finding the proper destination of a call.
When an IP phone makes a call, it sends an invite request to a proxy server. The phone itself doesn’t know what the digits mean, but the proxy server does.
The proxy server routes the request within the network, to a remote proxy server, or to an “off-domain network,” such as the PSTN.
For more information on this, you could look at Nextiva Reviews since they offer SIP Servers.
Forward Proxy
A forward proxy is a server that sits between clients and servers within an internal network. When you send the data, they examine it to decide whether or not the connection should be made; this makes sure no information gets lost in translation!
Internal Network
Forward proxies are a great way to provide IP address security and give thorough administrative control for your internal networks, but forward proxies may not work well with end-users.
Transparent Proxy
Transparent proxies are additional software that can be installed on your computer.
It provides users with the same experience as if they were at home, being able to connect without knowing it and have their internet activity monitored by whoever has access to this information- which should always remain private!
Companies that want to provide a seamless user experience but also keep their employees in the dark about it can use transparent proxies.
Transparent proxies are well-suited for these companies because they’re more susceptible to SYN flood attacks than other types of proxy, which could happen if someone were savvy enough.
Anonymous Proxy
The anonymous proxy is an efficient way to protect your internet activity.
It works by accessing the web while hiding your identity, computer information, and location from third parties like advertisers who want access into our personal lives for profit margins!
It is important for users who want anonymity while browsing the internet to use a transparent proxy.
While they do provide some protection from discrimination or pushback, there are still drawbacks with this type of service and many view them as underhanded because you’re hiding your identity behind one computer screen but showing it in other places online where people can see everything else about themselves upfront.
High Anonymity Proxy
A high anonymity proxy is a lifesaver when you need to maintain your privacy.
The proxy server erases all traces of information before connecting with the site, ensuring that no one can identify who we are or what sites we visit!
This proxy server is perfect for users who need complete anonymity, and it’s one of the best ways to maintain privacy.
On the downside, if you use free services that have tracking software built-in then your activity can be traced back.
Data Center Proxy
Data center proxies are not ISPs, but they provide another form of internet service.
The user’s request is routed through a physical data center and then inputted by one or more servers in order to access the desired web pages.
Data center proxies provide an inexpensive and quick way to gather intelligence on a person or organization.
The downside is that the service does not offer high levels of anonymity, which may put your information at risk if you use this type for sensitive matters.
Distorting Proxy
A distorting proxy identifies itself as a server for the site and hides its own identity, usually by changing IP addresses.
Distorting proxies may be a good choice for those who want to hide their location and anonymity while accessing the internet.
This type of proxy can make it look like you’re browsing from certain countries, giving users an advantage in hiding not just themselves but also that of any associated proxies as well!
SSL Proxy
An SSL proxy is designed to protect data from being read by anyone other than the intended recipients.
It can be used in any situation where you need someone’s input or information, but they don’t want it accessible without their permission–such as when two parties communicate via email over long distances and would rather not reveal what was said on either end if given this option
With an encrypted connection between sender/receiver, no third party will ever know about anything sent during these conversations because both sides are protected by HTTPS encryption.
Residential Proxy
A residential proxy is used to route all your internet traffic through a single device.
This way, you can’t get hacked and the IP address of this special computer won’t change with every connection or page load – as long as it remains physically plugged into an outlet!
Residential proxies allow users to block ads that come from competitors or bad actors on their websites.
They’re also more trustworthy than other types of proxy servers – Residential Proxy Services only allows traffic in response to specific commands, so you can be sure what goes through the link is legitimate!
However, this option often costs more money than alternatives which makes it something worth considering before making your final decision.
Shared Proxy
With shared proxies, you can use an IP address that is in high demand and may be available to other people. The best part about it? You’ll appear browsing from a location of your choosing!
Shared proxies are a great option for those who don’t want to spend money, but need an easy connection.
The main advantage of shared-proxy services is their low cost and you can still get the service without having any speed limitations on your internet service provider’s end or anything like that because it will all come through one IP address which other people use as well too.
Public Proxy
A public proxy is a great way to hide your identity when browsing the web. It allows anyone with internet access and no login credentials, free of charge!
Public proxies are a great option for those who need anonymity and speed.
They’re also free, but you run the risk of having your information accessed by other people on the internet when using one as well!
Rotating Proxy
A rotating proxy is a server that assigns an IP address to each user who connects.
As users are given the unique opportunity for internet connection, they can be assigned one from this system’s pool of machines in preference over their personal devices or laptops with WiFi-enabled.
Rotating proxy services are the perfect option for those who need to do a lot of high volumes, continuous web scraping.
These anonymous tools allow you to return again and again without being exposed by your identity or data on public proxies.
However, there’s always an element of risk when using rotating proxies that some might contain shared resources that could give away everything you’re doing online!
Reverse Proxy
A reverse proxy is a simple and effective solution for addressing the efficiency problems that arise when load balancing web servers.
Reverse proxies act as middlemen between your users’ browser requests, which are sent by networked computers on behalf of clients in order to serve up content at their endpoints (i.e., HTML files), with origin server responses so you can get faster page loads without having multiple copies running around!
Reverse proxies are a good option for websites that need to balance many incoming requests.
Reverse Proxies can help reduce bandwidth since they act like another web server and manage all the traffic coming in, but there is a potential security risk on your system if an attacker penetrates through it.
Network administrators might need beefing up or repositioning their firewall depending on what type of reverse proxy you have!
What Are Proxies and Their Main Benefits?
The benefits of using a proxy have been extensive and will help your business tremendously.
Not only can they increase productivity, but proxies also come with several other advantages such as increased security for both yourself and the information you’re working on behalf of.

- The internet is a vast and wild space, but with content filtering proxies you can shield your young children from some of the more extreme sites.
- Anonymous and high anonymity proxy servers allow you to surf the web without being tracked. You can find a variety of these types, like VPN or TOR connections for example that will mask your IP address so sites don’t know where traffic is coming from – helping keep things more private online than ever before!
- With a little caching, you can speed up your browsing next time and save on bandwidth costs.
- A proxy is a great way to get around any content restrictions you might find on the internet. You can also use it as an evasion tool for those who want their network blocked!
- Web proxies are a web designer’s best friend. They’re free, easy-to-use, and allow you to access the internet from behind an IP address that is not yours without having another monthly fee tacked onto your bill!
Proxy Server & IP Adress
Proxy Servers are also used by businesses to augment their overall data handling capabilities.
Often times, there are limits that receiving servers have come from a proxy IP address; however, with a proxy server, the IP address is different.
This method adds to the data handling and exchange capabilities of companies that don’t have an army of servers at the ready at all times.
There are other proxy web servers available as well, although they are not as common. At the end of the day, a proxy server is typically used to limit the information that is accessed or to track the usage of a particular user or user.
Primarily used in a business setting, proxy servers can be used in a home setting as well – particularly by parents hoping to limit the amount of offensive material their children have access to.
FAQ – What Are Proxies?
What are proxies used for?
A proxy server is a program that acts as an internet firewall and web filter.
A web proxy server can be used by individuals, companies, or organizations to protect themselves from the bad stuff out there on social media networks like Facebook, YouTube, etc., while also protecting their proxy users with restricted settings for content filtering at workplaces too!
Are proxies legal?
The use of a proxy web server is legal and it can be used for many things.
Proxies have been employed by organizations to enable remote work, set up support systems outside your network’s boundaries while protecting both local networks as well as those on the Internet from malicious content streaming in through clips that may not always comply with country laws or regulations. own
What is the difference between proxy and VPN?
A proxy is a simple, low-cost way to access the internet and protect your identity while doing so.
It’s ideal for basic functions like anonymous web browsing or managing content restrictions; however, it does not provide encryption of all network traffic which makes it less secure than other methods such as VPN connections.
Are proxies faster?
The Residential Proxies will be a huge benefit for those scraping the web, as they make it easier and faster.
This makes them perfect to use on any website that may block your IP address from accessing certain parts of their site or even delete what you are trying to scrape in some cases!